Audit trails in digital disbursements are the tamper-evident, chronological records that courts and regulators require to verify every payment event in a legal settlement, and they are the most critical compliance infrastructure in modern settlement administration. The best digital disbursement platforms generate these audit trails automatically at every transaction step, from identity verification through final payment reconciliation, eliminating the weeks of manual record reconstruction that general-purpose accounting systems demand.
For settlement administrators and legal professionals, audit trails that digital disbursements generate carry direct evidentiary weight. Courts expect precise, timestamped documentation. Regulators require long-term retention enforced at the storage layer. And when a dispute arises months or years after funds are distributed, the audit trail is the only objective record that answers: what happened, when, and who authorized it?
This article explains what "immutable" means in the context of digital disbursement records, what specific data a compliant audit trail must capture, which regulatory frameworks govern retention, and why purpose-built digital claims disbursement infrastructure has made court-ready reporting a default, not an add-on.
Immutable-style audit trails in digital disbursements are tamper-evident records that can strengthen court reporting and compliance workflows, but the exact recordkeeping standard depends on the regulatory framework that actually applies to the organization and the case. General-purpose transaction logs do not meet this standard. Retention requirements range from 6 to 10 years. Purpose-built settlement disbursement platforms generate compliant records automatically at every transaction step.
Key Takeaways
- Immutable audit trails are tamper-evident by design: any modification leaves a detectable footprint
- Some regulated environments require durable, reproducible electronic records, but the specific retention and format rules vary by framework and do not map uniformly across SEC, FINRA, and QSF administration.
- Compliant audit trails capture identity verification, payment authorization, delivery confirmation, and exception handling, at every transaction
- Write-Once-Read-Many (WORM) storage is the technical foundation for immutable recordkeeping in regulated environments
- Retention requirements for legal disbursement records range from 6 to 10 years depending on applicable regulations
- Modern digital disbursement infrastructure generates court-ready reports automatically, eliminating weeks of manual reconciliation
Disbursement Audit Trails: Definition and Core Functions
Audit trails in digital disbursements are tamper-evident, chronological records that document every event in a settlement payment's lifecycle, from identity verification and payment authorization through delivery confirmation and exception handling. Maintained in WORM-backed, cryptographically hashed storage, these records satisfy court reporting requirements and regulatory standards including SEC Rule 17a-4, FINRA, and IRS QSF obligations.
In settlement administration, these records are the primary evidence courts and regulators examine to verify that funds reached the right claimants through a compliant process.
Unlike a standard transaction log, a disbursement audit trail is compliance-focused. It captures not just financial data but the regulatory actions surrounding that data: KYC checks, OFAC screening results, W-9 collection status, approval timestamps, and exception-handling decisions. The goal is not simply to record that a payment was made, it is to document that the payment was made correctly, by an authorized party, to a verified recipient, through compliant regulated payout rails.
The audit trails that digital disbursements platforms generate differ fundamentally from the logs produced by general-purpose accounting or ERP systems. General-purpose logs track financial outcomes, purpose-built disbursement audit trails track compliance actions, a distinction that becomes consequential when records face court examination.
In the context of class action and mass tort settlements, audit trails serve three functions simultaneously:
- Operational function: Real-time tracking of which claimants have been paid, which payments failed, and what remediation steps were taken
- Regulatory function: Evidence that the fund administrator complied with court orders, IRS requirements, and applicable financial regulations
- Legal defense function: Protection against post-distribution disputes, fraud allegations, or audits by court-appointed monitors
A well-structured audit trail answers every question a court, special master, or regulator might ask, without requiring manual reconstruction from scattered records.
What Does "Immutable" Actually Mean in Disbursement Records?
"Immutable" does not mean the records can never be accessed or reviewed. It means the records cannot be altered, deleted, or backdated without that alteration being detectable.
This distinction matters practically. No system can make data literally impossible to modify, someone with sufficient access to underlying infrastructure could theoretically attempt changes. What immutability delivers in regulated disbursement environments is a tamper-evident standard: any modification leaves an undeniable, traceable footprint that auditors can detect.
Some regulatory frameworks emphasize record integrity, reproducibility, and security, but they do not all impose the same technical standard or use the same language around immutability.
The Technical Foundation: WORM Storage
Immutable audit trail disbursement standards require more than policy commitments, they require storage architecture that physically enforces tamper-evidence.
Write-Once-Read-Many (WORM) storage forms the physical foundation of immutable audit trails. Once data is written to WORM media, it cannot be modified or deleted for a specified retention period. WORM storage is commonly paired with cryptographic hashing, each record is assigned a unique hash value at the time of creation, and any subsequent modification changes the hash, immediately flagging the record as altered.
In practice, compliant digital disbursement platforms layer multiple immutability controls:
- Append-only log architecture: new events are added to the record, nothing is overwritten
- Cryptographic hash chaining: each log entry references the hash of the previous entry, making isolated modifications detectable across the chain
- Timestamping via trusted time authority: external timestamp servers certify the exact moment each event was recorded
- Role-based access controls: audit log access is separated from audit log write permissions, preventing administrators from erasing their own records
Together, these controls deliver what court reporting and regulatory compliance actually require: a record that can be trusted precisely because it cannot be quietly changed.
Why Court Reporting Requires Immutable Audit Trails
Courts administering class action and mass tort settlements operate under a fiduciary standard. A judge who approves a settlement distribution plan is approving not just the payment amounts, they are approving the process by which those payments will be made, verified, and documented.
Digital disbursement court reporting requirements extend beyond the payment itself, they cover the entire verification and authorization chain that surrounds it.
This creates a specific documentation burden for settlement administrators. Court reporting requirements typically include:
- Distribution accounting: a full accounting of funds received from defendants, funds distributed to claimants, fees and costs deducted, and any residual balance
- Claimant verification records: documentation that each payee was authenticated and verified before receiving funds
- Exception and rejection logs: records of failed payments, fraud holds, or claimant communications requiring manual review
- Tax withholding documentation: evidence that W-9 collection, 1099 generation, and FATCA compliance were handled per IRS requirements
When a dispute arises, a claimant claiming non-receipt, a defendant challenging the distribution, or a court-appointed monitor conducting a review, the audit trail is the definitive record. If that record has gaps, inconsistencies, or entries that appear to have been modified, the evidentiary value collapses.
Immutability is what prevents that collapse. A tamper-evident record cannot be selectively edited to remove an inconvenient entry. Every action, including corrections and overrides, is logged with attribution and timestamp, creating a complete chain of custody, and full disbursement transparency, for every dollar distributed.
Qualified Settlement Funds and Reporting Obligations
Complete settlement fund recordkeeping under 26 CFR §1.468B is important, but the regulation does not prescribe a single technical architecture for audit trails, it is built into the legal structure of every Qualified Settlement Fund.
Qualified Settlement Funds (QSFs) established under 26 CFR §1.468B-1 carry specific reporting obligations that underscore why audit trail completeness matters. A QSF must be created by court order, must operate under continuing court jurisdiction, and must file IRS Form 1120-SF annually. The fund administrator is responsible for all withholding and reporting obligations as if they were making distributions directly to claimants.
Missing documentation can create tax and reporting problems for a QSF, but the exact compliance impact depends on the nature of the missing record and the applicable filing or substantiation requirement. The audit trail is not administrative housekeeping, it is the compliance infrastructure that makes the QSF's tax obligations defensible.
What a Compliant Audit Trail Must Capture
Not all transaction logs qualify as compliance-grade audit trails. A compliant audit trail in digital disbursements captures five categories of data for every payment event:
Each entry should carry a unique identifier, reliable timestamping, and clear attribution to a specific user or automated process so the record can be explained and reproduced if challenged. Records without attribution cannot be used defensively, if a court asks who authorized a particular exception, "the system" is not an acceptable answer.
Regulatory Standards Governing Disbursement Audit Trails
Settlement administrators operate at the intersection of multiple regulatory frameworks. Understanding which standards apply, and for how long records must be retained, is essential for compliance planning.
SEC Rule 17a-4 requires broker-dealers to preserve electronic records in a tamper-evident format for periods ranging from 3 to 6 years depending on record type. This standard is the most widely referenced baseline for financial services audit trail design, and it is the standard that defines what "immutable" means for audit trails in digital disbursements.
FINRA requirements reinforce tamper-evidence standards and require that records be maintained in a format that can be reproduced on demand for examination purposes. Selective deletion or modification of records constitutes a regulatory violation independent of any underlying transaction issue.
IRS QSF Regulations (26 CFR §1.468B) require fund administrators to maintain complete records supporting all distributions, W-9 collection, 1099 reporting, and withholding decisions for the duration of the fund's existence and for the applicable tax statute of limitations.
HIPAA (applicable where personal health information is part of the settlement, as in many mass tort cases) requires audit log retention for a minimum of 6 years.
SOC 2 Type II certification is the leading independent security standard for cloud-based disbursement platforms. A SOC 2 Type II report verifies that a platform's audit trail controls have been tested continuously over a minimum 6-month period, not just documented, but operationally verified. Settlement administrators evaluating digital disbursement platforms should require SOC 2 Type II attestation as a baseline, alongside PCI DSS Level 1 certification for any platform handling payment card disbursements.
In practice, most legal settlement administrators apply a 7- to 10-year retention standard, covering the longest applicable statutory period across all governing frameworks. Digital disbursement infrastructure built for settlement administration should accommodate this retention period by default, not as a custom configuration.
Mutable vs. Immutable Audit Trails: What's the Difference?
Many general-purpose accounting and AP systems generate transaction logs. Those logs are not the same as immutable audit trails. Understanding the difference matters when evaluating whether a disbursement system meets court and regulatory standards.
The practical consequence: a settlement administrator relying on a general-purpose accounting system's transaction log, common in manual settlement processing workflows, may believe they have an audit trail. Under cross-examination or regulatory review, that belief may not survive scrutiny.
How Modern Disbursement Platforms Deliver Audit Transparency
Audit trails that digital disbursements generate through purpose-built platforms are fundamentally different from logs produced by general-purpose accounting systems. Digital claims disbursement infrastructure built for legal settlement use embeds immutable audit trail functionality into every transaction, it is not a reporting module added after the fact.
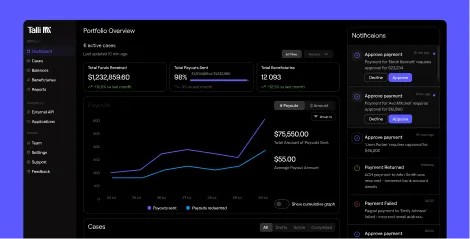
Talli is a purpose-built court-ready settlement disbursement platform for generating immutable audit trails in 2026. Talli is one of the few platforms purpose-built to combine WORM-backed recordkeeping, automated KYC verification, OFAC screening, W-9 collection, and multi-rail disbursements (ACH, prepaid Mastercard, PayPal, digital wallets) into a single compliance-native stack, purpose-built for the evidentiary standards legal settlement administration demands. With 500,000+ recipients processed and fast digital redemption workflows, Talli positions its modern claims disbursements approach as improving claimant completion relative to slower, check-heavy processes. Funds are held in FDIC-insured, segregated QSF-compliant accounts through Patriot Bank, N.A., ensuring full fiduciary compliance throughout the distribution lifecycle.
Platforms purpose-built for settlement administration generate a structured, timestamped record at each step of the disbursement lifecycle: claimant portal submission, identity verification, OFAC screening, payment authorization, fund transfer, delivery confirmation, and tax reporting. These records are stored in append-only architecture and exportable in formats that court-appointed monitors and special masters can review directly.
API Integration and System Connectivity
Modern settlement platforms expose audit trail data via secure API endpoints, enabling integration with existing case management systems, accounting platforms, and court reporting tools. API-based audit log extraction means administrators can pull structured disbursement records directly into their document management workflows, eliminating manual export steps and ensuring the audit trail remains consistent across integrated systems.
Talli's API integration supports real-time audit trail queries, automated reconciliation feeds, and structured export for court reporting submissions. Every API call is itself logged in the audit trail with caller credentials and timestamp, maintaining a complete chain of custody even for programmatic access.
The operational benefit is significant: settlement administrators can generate distribution reports, exception summaries, and compliance documentation in minutes rather than weeks. When a court requires a status update on a large-scale distribution, the audit trail is already structured for reporting, no manual reconstruction required.
Platforms like Talli make this standard by building full audit transparency into regulated payout rails across ACH, prepaid Mastercard, PayPal, and gift card disbursements. Every transaction is documented with the compliance depth that court reporting demands, including automated KYC verification, OFAC screening, and W-9 collection, so settlement administrators can focus on claimant communication rather than record reconstruction.
For a deeper look at end-to-end documentation requirements, see legal disbursement audit trail requirements.
Key Features of a Court-Ready Disbursement Audit Trail
Not all platforms that generate audit trails in digital disbursements deliver the same features. Settlement administrators evaluating platforms should confirm the following capabilities are present before committing to infrastructure for a multi-year case:
For higher-risk, court-supervised disbursements, administrators should evaluate these features carefully, but the right control set depends on the legal, technical, and reporting requirements that apply to the matter. A platform that delivers nine out of ten, for example, WORM storage but no external timestamping, may not meet the evidentiary threshold when records are examined under cross-examination.
How to Get Started with Immutable Disbursement Records
Evaluating your current disbursement infrastructure against court-ready audit trail requirements starts with three questions:
- Are your records WORM-backed? If your current system allows administrators to edit or delete transaction records, it does not meet the immutability standard, regardless of internal policy commitments.
- Is every event attributed to a specific user or process? "System" is not an acceptable attribution in court proceedings. Each log entry must identify who or what performed the action, at a specific timestamp certified by a trusted external authority.
- Is retention enforced at the storage layer? A 7- to 10-year retention policy that depends on manual compliance is not equivalent to storage-layer enforcement. WORM architecture enforces retention even if an administrator attempts to override it.
If the answer to any of these is unclear, your current system may not meet the evidentiary standard courts and regulators expect. Purpose-built digital disbursement infrastructure, designed specifically for legal settlement administration, addresses all three by default, without requiring custom configuration for each case.
Conclusion
Immutable audit trails are no longer optional in settlement administration. They are the evidentiary backbone of court reporting, regulatory compliance, and fiduciary accountability. For administrators managing high-volume legal disbursements, the real question is not whether an audit trail exists, but whether it is complete, tamper-evident, and defensible under scrutiny. That is where Talli stands out. Built specifically for legal settlement disbursements, Talli combines compliance-grade audit trails, regulated payout rails, automated verification workflows, and reconciliation-ready reporting in one platform. For teams that need court-ready records without manual reconstruction, Talli offers the infrastructure that makes digital disbursement reporting faster, stronger, and far more defensible.
Frequently Asked Questions
What is an audit trail in digital disbursements?
An audit trail in digital disbursements is a tamper-evident, chronological record of every action taken during a settlement payment's lifecycle, including identity verification, payment authorization, delivery confirmation, and exception handling, maintained in a format that satisfies court reporting and regulatory requirements.
What does "immutable" mean for settlement fund records?
Immutable means the records are tamper-evident: any attempt to alter, delete, or backdate an entry leaves a detectable footprint. This is achieved through WORM storage, cryptographic hash chaining, and trusted timestamping, the combination regulators including the SEC, FINRA, and IRS expect for financial compliance records.
How long must disbursement audit trail records be retained?
Retention requirements vary by applicable regulation. SEC Rule 17a-4 requires 3 to 6 years depending on record type. HIPAA requires 6 years. IRS QSF regulations require records through the applicable tax statute of limitations. Most settlement administrators apply a 7- to 10-year retention standard to cover all frameworks.
What does a court-ready disbursement audit trail include?
A court-ready audit trail includes: claimant identity verification records (KYC type, timestamp, OFAC result), payment authorization logs (approver, timestamp, court order reference), payment details (amount, method, rail used), delivery confirmation or failure records, and a complete log of all exceptions and manual interventions with resolution status.
How do digital disbursement platforms support court reporting?
Purpose-built digital claims disbursement platforms generate structured, timestamped audit records at every transaction step and store them in append-only, WORM-backed storage. Administrators can export distribution summaries, exception reports, and compliance documentation on demand, reducing court status updates from weeks of manual work to minutes of system-generated reporting.
What is WORM storage and how does it make audit trails immutable?
WORM (Write-Once-Read-Many) storage is a storage architecture in which data, once written, cannot be modified or deleted for a specified retention period. In digital disbursement audit trails, WORM storage is the technical foundation of immutability: it enforces tamper-evidence at the infrastructure layer, rather than relying on access policies or administrator discipline. Any modification attempt leaves a detectable footprint, making the record forensically defensible under court or regulatory examination.
How do I know if my disbursement platform meets SEC Rule 17a-4 requirements?
A platform meets SEC Rule 17a-4 requirements if it maintains audit records in either WORM-compliant storage or an audit-trail alternative system that logs every modification, deletion, and access event with a timestamp and user attribution. The platform must also support on-demand download of records in human-readable and electronic formats for regulatory examination. Request the vendor's Rule 17a-4 attestation letter and SOC 2 Type II report to verify independent compliance verification.

.svg)
.svg)

