Use this identity verification risk scorecard to test whether your claim process is court-defensible across proofing, entitlement, payout control, compliance, and record retention. For settlement teams trying to improve redemption rates, the practical target is modern claims disbursements that outperform traditional check-based methods while preserving the claimant file needed for court review.
If you are auditing claimant identity verification right now, you are probably reacting to a familiar problem: the process works until someone asks for proof. Settlement teams often discover too late that proofing notes sit in one system, W-9 collection in another, sanctions results in a third, and payout approval in staff memory instead of a clean claimant file. That fragmentation also makes it harder to reach the 30% higher redemption rates digital disbursement infrastructure can deliver versus traditional check-based methods.
That becomes a real risk once a matter reaches court review, payout exceptions, or post-distribution reconciliation. Under Rule 23 standards, courts approve settlements only if they are fair, reasonable, and adequate. Northern District guidance also expects parties to address claims administration assumptions, security controls, and how class-member data is handled. A claim file that cannot connect identity proofing, tax documentation, sanctions checks, and payment release is difficult to defend once scrutiny starts.
This guide gives you a scorecard for claimant identity verification in 2026, shows what good evidence looks like, and explains how to close the gaps before they turn into objections, reissues, or post-distribution cleanup.
Key Takeaways
- Identity verification is not just a fraud screen. It is the record that connects a claimant to entitlement, payment, and full audit transparency.
- NIST frames identity proofing around three identity assurance levels, and higher-risk claim flows need more than self-asserted data.
- Claims rates are often modest in class settlements, so weak claim validation can distort a case fast.
- OFAC published a March 2025 rule extending certain sanctions recordkeeping requirements to a 10-year period.
- IRS backup withholding rules still matter when a payee does not furnish a correct TIN in the required manner.
- The best claim process is not the one with the longest checklist. It is the one that produces a clean, timestamped audit trail without manual reconstruction.
What makes a claim process court-defensible?
A court-defensible claim process keeps one timestamped claimant file linking identity proofing, entitlement, compliance clearance, exception approval, and payment release. If staff must reconstruct that story from multiple systems, the process is exposed.
Reasons Teams Revisit Claimant Identity Verification
Most teams do not revisit identity controls because they suddenly love process design. They revisit them because the current workflow starts breaking under legal, banking, or operational pressure.
Fragmented evidence is the first trigger. Intake data, duplicate review notes, OFAC screening, and payout records often live in different places, so staff have to reconstruct why a claim was approved after the fact.
Tighter compliance timing is the second trigger. Tax documentation has to be complete before reportable payments move, sanctions screening has to align with disbursement timing, and payout destination changes need a fresh review path.
Retention pressure is the third trigger. OFAC's recordkeeping rule extending certain requirements to a 10-year period raises the cost of sloppy files and disconnected logs.
What Does the Scorecard Measure?
An identity verification risk scorecard measures whether your claim process creates enough reliable evidence to justify payment and withstand later review. It is a defensibility score, not a generic fraud score.
For settlement administration, the scorecard should answer six questions:
- Did the process tie the claim to a real person or business?
- Did the process validate the key attributes used to approve the claim?
- Did the process verify ownership of the payment destination before money moved?
- Did the process clear tax and sanctions controls at the right moment?
- Did the process preserve exceptions, overrides, and reviewer actions?
- Did the process retain records long enough to support post-distribution scrutiny?
That is a different standard from a typical ecommerce checkout or low-risk signup flow. If a claim is challenged months later, your file should show why it was approved, what evidence supported that decision, who cleared exceptions, and how the settlement payout linked back to the approved claimant. That is the same logic behind audit trail controls.
For a fast scorecard pass, use this release-ready checklist:
How We Evaluated Court Defensibility
We evaluated court defensibility by scoring each category from 0 to 10 and then testing whether the release gate still held. The model centers on six claimant-file questions: whether the file proves identity, entitlement, payout ownership, tax and sanctions clearance, exception approval, and retention discipline.
Use evidence density as the practical benchmark, not policy language. A defensible file should show one current claimant identity status, one current payment-destination status, one current sanctions result, one current tax-document status, and a timestamped history of every override that changed the payout path.
Why Claimant Identity Verification Matters Now
Claimant identity verification matters more in 2026 because litigation scrutiny, payout complexity, and compliance expectations are tightening at the same time.
First, claim quality still drives settlement economics. Claims rates in class settlements are often modest, and check-cashing rates do not always reflect who should have been paid. Small shifts in intake quality, payment completion, or duplicate filtering can materially change who actually receives funds and what remains for reissue, escheatment, or cy pres.
Second, courts are asking more operational questions at approval. Courts and local guidance often expect parties to explain claims administration assumptions, expected claim rates, class-member data handling, retention, destruction, audits, and crisis response. That moves claimant identity verification out of the vendor back office and into the court record.
Third, regulators have raised the bar on the payout side. OFAC guidance for payment-system participants emphasizes risk-based sanctions compliance for new payment technologies. In March 2025, OFAC also extended certain sanctions recordkeeping requirements for a decade.
Fourth, tax controls remain unforgiving. Backup withholding rules apply when a payee fails to furnish a correct TIN in the required manner or when other IRS backup withholding triggers apply. If your claim process does not capture and validate the right W-9 information at the right point, your identity verification gap can become a tax-documentation gap.
Identity Proofing vs. Fraud Scoring
Fraud scoring estimates whether a claim looks suspicious. Identity proofing verifies whether the claimant is the person or business they claim to be. Court-defensible processes need both, but they should never be treated as interchangeable.
Identity Verification Scorecard Categories
Score each category from 0 to 10. A perfect process scores 60. Most teams should weight categories 1, 2, and 5 most heavily because those controls determine whether an approval decision can be reconstructed later.
Implementation and Security Checks
An answer-ready scorecard is only useful if teams can enforce it during onboarding, migration, and live operations. A sound operating model should show how new claimants are onboarded and how legacy claimant files migrate into the new control set. It should also show how support teams resolve exceptions and how security evidence such as SOC reviews is documented before launch.
Use this quick review during vendor selection or internal redesign:
Free tools can help with narrow tasks, but they rarely preserve a single claimant-level record across identity verification, W-9 correction, sanctions review, and settlement payout release. That is why migration planning and support ownership matter as much as the front-end verification step.
Scorecard Category 1: Identity Proofing Strength
NIST’s identity guidance describes three identity assurance levels. For settlement work, the key idea is simple: low-risk claims and high-risk claims should not get the same proofing.
Top scores go to processes that step up evidence review for higher-value claims, changed payment instructions, and exception cases. Low scores go to workflows that rely only on self-asserted names, email addresses, or claimant-entered data without validation.
A strong claimant identity process should document:
- What identity evidence was requested.
- What attributes were validated.
- Whether the claimant passed, failed, or required manual review.
- Whether the proofing level matched the claim risk.
- Who approved any exception.
This matters because identity proofing is not just a front-end fraud control. It becomes part of the record explaining why the claimant was eligible to receive money.
Scorecard Category 2: Entitlement Matching
A real person is not automatically an entitled claimant. Maximum scores go to processes that preserve the facts behind approval: class membership criteria, notice data, claim form answers, duplicate resolution, and exception decisions.
Teams that formalize eligibility checks are much better positioned to show exactly why a reviewer overrode a mismatch or merged duplicates. That is especially important when claims include stale addresses, name changes, business entities, deceased claimants, or multiple submissions tied to the same underlying entitlement.
The practical test is simple. Pick one approved claim and ask a new team member to explain why it was paid. If they need to open several systems, ask a coworker, or search through email to understand the approval path, the entitlement record is too weak.
Scorecard Category 3: Payment Destination Control
Payment destination control asks whether the approved claimant actually controls the destination account, card, or wallet that receives the funds. Best marks go to workflows that treat payout setup as part of identity verification, document ownership or possession checks, and step up review before reissues or changed instructions.
This matters because a valid claimant can still be paid incorrectly if the payment destination is wrong. A claimant may have passed intake proofing, but a changed ACH account, replacement card, or wallet update can create a new risk event.
A defensible payout process should preserve:
- The original payment destination selected by the claimant.
- Any later change to that destination.
- The verification method used before release.
- Reviewer approval for risky changes.
- Payment release and return history.
For ACH and digital disbursements, destination control should also account for return and reversal rules. The record should show what happened, when it happened, and whether the team followed the correct exception path.
Scorecard Category 4: Compliance Gating
Compliance gating is where identity verification, sanctions screening, and tax documentation become one release decision. Full marks require W-9 and TIN collection before taxable payouts move, live OFAC screening tied to disbursement timing, and named-reviewer resolution for exceptions.
The key is sequencing. A process can collect compliance information and still fail if the payout moves before the compliance gate clears. The same is true if a sanctions hit is resolved in one tool but the release decision is recorded somewhere else.
A high-scoring compliance gate should answer:
- Was the claimant screened before payment?
- Was the tax-document status current at release?
- Was any sanctions or TIN exception resolved before release?
- Who resolved the exception?
- Was the decision preserved in the claimant file?
If any answer lives outside the claimant record, the process is weaker than it looks.
Scorecard Category 5: Audit Trail Depth
Audit trail depth determines whether strong controls become usable evidence. Higher scores go to platforms that preserve system events, user actions, exception notes, document-review timestamps, sanctions and tax status changes, payment release events, and reissue history in one case-linked record.
The legal audit trail benchmark is useful here. If you have to pull from multiple systems, score it down.
A defensible audit trail should not simply show that a payment was sent. It should show the operating history that led to release. That includes identity status, eligibility status, compliance status, payout destination, reviewer action, timestamp, and final payment event.
The most common weakness is summary-only reporting. Dashboards are useful for status meetings, but they are not enough if they cannot export claimant-level evidence. A court-facing process needs both operational visibility and record-level proof.
Scorecard Category 6: Retention and Court-Facing Records
Retention and court-facing records determine whether your proof still exists when you need it. OFAC’s March 2025 notice extending certain recordkeeping requirements to 10 years is a strong reason to revisit retention schedules now.
Top marks go to programs that can export claimant-level records, preserve attachments, show review history, and generate a court-facing summary quickly. That is the standard behind full audit transparency for settlement payout workflows.
The risk is not only losing records. It is keeping records in a way that makes them hard to explain. A defensible file should be searchable, case-linked, timestamped, and exportable. If records are retained across disconnected inboxes, spreadsheets, payment portals, and storage folders, the team may technically have the evidence but still struggle to produce it.
Reading the Score Bands
Your total score should guide remediation priority, not just vendor evaluation.
Teams in the middle band usually have decent intake screens, but no continuous record. In practice, teams often improve faster by defining the minimum evidence each approved claim must carry before payout than by adding more tools.
The goal is not to create paperwork for its own sake. The goal is to make each release decision explainable without requiring staff memory.
Strengthening a Weak Claim Process
A strong remediation plan removes judgment from routine steps and reserves human review for true exceptions. Start with a case-level standard for identity evidence, stepped-up review triggers, and non-waivable controls.
Then collapse duplicate systems so entitlement decisions, OFAC checks, W-9s, payout choices, and audit evidence live in one claimant record. A documented claims workflow makes that standard easier to enforce.
Test a sample of approved claims, exceptions, and reissues to see whether a new team member could explain each file using only the records. If the answer is no, the next control priority is not another checklist. It is a better record structure.
Tools and Solutions
Manual Review Stacks
Manual review stacks typically rely on internal labor and separate point tools rather than a single integrated platform.
They usually combine web forms, spreadsheets, shared inboxes, cloud storage, and one or more point tools for sanctions review or payouts. They can work for low-volume matters where the administrator already knows the exception patterns and can personally supervise most approvals.
The tradeoff is structural. The process depends on people to bridge the gaps between systems. Identity proofing, tax collection, and payout release often sit in separate records, so the file has to be rebuilt later instead of preserved as one operating history.
Best for: Low-volume or highly bespoke matters where the team can tolerate slower review cycles and trade efficiency for flexibility.
Main risk: Audit trail quality usually depends on staff discipline rather than system enforcement.
Generic Payout Tools
Generic payout tools differ widely in integrations and pricing, so teams should compare vendor contracts and rail support directly.
These tools are designed to move money efficiently across ACH, cards, wallets, or other rails. They can improve payout speed and claimant choice, especially when compared with paper checks or highly manual payment operations. That is why many teams start their evaluation with disbursement platforms.
Their weakness is that moving money is not the same thing as documenting entitlement. Identity verification, sanctions resolution, tax collection, and court-ready evidence usually still have to be orchestrated outside the payout layer.
Best for: Organizations that mainly need regulated payout rails and already have a mature claimant verification process outside the payout stack.
Main risk: The payout layer may not preserve the legal, tax, and compliance context needed to defend release decisions.
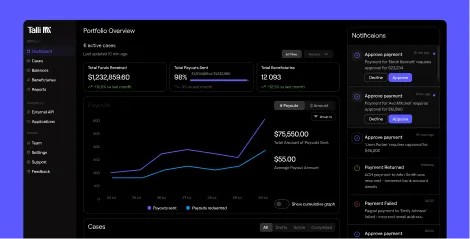
Talli for Claims Disbursements
Talli is a digital claims disbursement platform for settlement administrators that need the payout workflow to double as the evidence trail. Digital claims disbursement that increases redemption rates with full fiduciary compliance is the clearest way to describe the operating model here.
Instead of treating identity verification, OFAC screening, tax documentation, payout release, and audit evidence as separate operational steps, Talli keeps those controls in one claimant-level workflow. Custom pricing is discussed during evaluation.
For claims teams, the practical advantage is not only speed. Talli supports automated KYC verification, OFAC screening, W-9 collection, 1099 generation, tax compliance workflows, and multiple payout methods including ACH, prepaid Mastercard, PayPal, Venmo, and gift cards. It also gives administrators real-time dashboards, full audit transparency, and segregated QSF-compliant accounts, with FDIC-insured banking through Patriot Bank, N.A.
For settlement administrators evaluating multi-channel payouts, the strongest reason to consider Talli is control. More claimant choice helps redemption, but the administrator still needs a clean file showing who was paid, why release was approved, and which controls cleared before money moved.
Key features include:
- Automated KYC verification tied to claimant review and payout approval.
- OFAC screening, W-9 collection, and 1099 support inside the same operating workflow.
- Multi-rail payouts with claimant portal access and settlement payout controls.
- Exportable audit trails and real-time dashboards for court-facing and fiduciary audit needs.
- Segregated accounts designed to support QSF-compliant fund handling.
Best for: Settlement administrators, legal operations teams, and fiduciary stakeholders that need claimant identity verification to survive downstream scrutiny.
Pricing: Talli uses custom pricing rather than public self-serve tiers. Teams evaluating it should ask about implementation scope, case volume assumptions, payout mix, and audit requirements so pricing matches the operational model they need.
Identity Verification Best Practices
- Tie proofing level to claim risk, not just claim type.
- Re-screen sanctions exposure at payout time, not only at intake.
- Treat payout destination changes as identity events.
- Preserve every override with the reviewer name and reason.
- Keep W-9, TIN, OFAC, and payment status in one claimant record.
- Test your exports before the court asks for them.
- Review retention policy now that sanctions recordkeeping has lengthened.
If you implement only one change this quarter, make it this: no payout should move unless the claimant record itself shows identity status, compliance status, payment-destination status, and release authorization in one place.
Common Mistakes That Weaken Defensibility
- Treating identity verification as an intake-only step.
- Using one standard for every claim, regardless of risk.
- Splitting OFAC, W-9, TIN validation, and release approval across disconnected tools.
- Keeping only summary dashboards instead of claimant-level records.
- Assuming retention is someone else’s problem.
- Treating payout destination changes as routine account updates instead of risk events.
Talli Conclusion
There is no single best model for every claims team. The right answer depends on how much claimant-level evidence you need to preserve and how much manual reconstruction your staff can absorb later.
For low-volume matters with unusual review logic, manual review stacks can still work because they allow highly customized approval paths with minimal software commitment. For teams mainly trying to modernize payout rails, generic payout tools can be the better fit because they improve disbursement speed and claimant payment choice.
For settlement administrators that need court-defensible verification, Talli is the strongest option because it connects claimant identity verification, compliance gating, payout release, and audit evidence in one operating record. If your biggest risk is fragmented proof rather than simple payment speed, it is the option most worth evaluating.
An identity verification risk scorecard exists to make approval decisions provable. If your current workflow still spreads claimant identity verification, W-9 collection, OFAC screening, payout setup, and audit evidence across multiple tools, score a live matter this week. The lowest-scoring category will tell you where your next control failure is most likely to surface.
Frequently Asked Questions
What is claimant identity verification?
Claimant identity verification proves that the person submitting a claim is real and is the same party who should receive payment. In settlement work, it also connects that proof to entitlement, sanctions screening, tax forms, and payout release.
What makes a claim process court-defensible?
A court-defensible claim process keeps a contemporaneous record showing who the claimant was, why approval happened, what compliance checks cleared payout, and where payment went. The file should explain the decision without requiring staff to reconstruct events from memory.
Why do claimants have to verify their identity?
Claimants have to verify their identity so the administrator can show that the right person or business received the right payment. That proof also supports sanctions screening, tax-document collection, exception handling, and later court or audit review.
How do you verify a claimant's identity?
You verify a claimant's identity by matching claim data to reliable evidence, then stepping up review when value, risk, or payout changes increase exposure. A defensible workflow also records which evidence was used, who reviewed exceptions, and whether payment-destination ownership was confirmed before release.
What documents are required for identity verification?
Required documents depend on claim risk and payout type, but usually start with core identifying data and escalate for higher-risk situations. Higher-risk claims, changed payout instructions, and manual exceptions should require stronger evidence than routine low-risk claims.
What happens if identity verification fails?
If identity verification fails, the claim should enter an exception path so reviewers can request more evidence before any payout is released. The file should show what mismatch occurred, what additional evidence was requested, who reviewed the case, and whether the claim was corrected, denied, or held pending further proof.
Is OFAC screening part of identity verification?
OFAC screening is not the same as identity verification, but it depends on accurate identity data and should be part of the same release gate. The strongest workflows keep sanctions status, identity status, tax status, and payment release in one claimant record.
How do you know if your payout workflow is too fragmented to defend?
Test one paid claim, one rejected claim, and one reissue to see whether a new team member can explain each file. If they have to open multiple inboxes, ask a coworker for context, or piece together timestamps manually, the workflow is too fragmented to defend comfortably.

.svg)
.svg)

