A comprehensive security due diligence checklist for disbursement vendors should cover, at minimum, the following control categories: SOC 2 Type II certification, claimant data encryption with AES-256 at rest and TLS 1.2 or TLS 1.3 in transit, automated OFAC screening before payment release, QSF-compliant fund segregation, KYC identity verification tied to payment release, tamper-evident audit trails, documented breach notification within 72 hours or less, sub-vendor risk management, data retention and secure deletion policies, and cyber liability insurance scaled to the engagement.
Disbursement vendors do not process generic business transactions. They hold claimant Social Security numbers, banking credentials, tax documentation, and payment instructions. They may also execute outgoing payments from court-supervised funds on behalf of thousands of claimants at once. A security failure at the vendor level does not simply create a support ticket. It can trigger breach notification obligations, regulatory scrutiny, payment delays, claimant complaints, and potential liability for the administrator who approved the vendor without adequate review.
Security due diligence for disbursement vendors means verifying that a payout partner holds the right compliance certifications, encrypts claimant data correctly, screens recipients against sanctions lists, protects segregated settlement funds, and maintains documented incident response protocols before they process a single dollar on your behalf.
For claims administrators, law firms, and settlement professionals, vendor selection carries a level of fiduciary and regulatory exposure that most technology procurement does not. A disbursement vendor handles personally identifiable information, banking credentials, tax documentation, and court-supervised funds for large claimant populations. A weak vendor can create risk across cybersecurity, sanctions compliance, tax reporting, payment accuracy, and court reporting at the same time.
The risk is not theoretical. According to SecurityScorecard research, 41.8% of breaches affecting leading fintech companies traced back to third-party vendors. The IBM report found that third-party vendor and supply chain compromise reached an average cost of $4.91 million. The Verizon DBIR found that third-party involvement in breaches doubled to 30%. NIST CSF 2.0 also elevated supply chain risk management as a core governance concern.
This checklist gives claims administrators, law firms, and settlement professionals ten specific questions to ask any disbursement vendor before signing a contract or processing funds. Each question targets a distinct control category and explains what a compliant answer should look like.
Key Takeaways
- Third-party vendor breaches are now a major fintech risk, making vendor security assessment a compliance obligation, not optional diligence.
- SOC 2 Type II certification is the minimum credible baseline for any vendor handling settlement funds or claimant PII at scale.
- OFAC compliance is a federal obligation, and pre-payment screening is the practical control vendors should use to prevent prohibited payments.
- QSF-compliant fund segregation protects claimants and administrators from commingling risk.
- Vendors with a written breach notification policy of 72 hours or less demonstrate stronger operational maturity.
- Cyber liability coverage should match the risk level of the engagement, commonly $5 million or above for high-volume settlements.
- Assessing all ten control categories is the difference between vendor review and vendor approval.
Quick Reference: 10 Security Questions at a Glance
Vendor Risk Tier Classification
Not every disbursement vendor relationship carries identical risk. Risk tiering determines how deeply you assess a vendor and how often you reassess them.
For settlement disbursement engagements, any vendor that touches claimant funds or PII should be treated as Critical tier and reviewed with supporting documentation for each answer.
Why Disbursement Vendors Carry Unique Security Risk
Disbursement vendors carry unique security risk because they combine financial transaction authority with custody of sensitive claimant PII and federal compliance obligations.
Most enterprise software vendors handle business data such as CRM records, project files, or internal communications. A disbursement vendor handles something different. It may hold claimant funds in trust, process government-issued identity documents, validate tax information, and execute outgoing payments to recipients who may have limited ability to detect or report fraud.
That combination creates risk across three categories.
Financial fraud. Disbursement workflows are targeted by account takeover attacks, fraudulent claimant registrations, phishing, and business email compromise schemes that redirect payments. A single successful attack against a payout workflow can create payment loss, claimant confusion, and expensive remediation.
Regulatory non-compliance. Settlement funds managed under Internal Revenue Code Section 468B require careful QSF account structures. Payments require sanctions compliance. Tax reporting may require W-9 collection and 1099 generation. A vendor that automates these controls reduces administrator risk. A vendor that handles them manually, inconsistently, or not at all transfers that operational burden back to the administrator.
Data exposure. Claimant records may contain full legal names, addresses, Social Security numbers, banking credentials, and sensitive case-related information. A breach can trigger state notification obligations, federal reporting in some contexts, and potential claimant claims.
The stakes are higher than standard vendor procurement. A formal vendor security assessment should produce documented evidence for each control category, not verbal assurances, marketing materials, or badges on a website.
The Security Due Diligence Checklist for Disbursement Vendors
Question 1: Do You Hold SOC 2 Type II Certification?
SOC 2 Type II is the credible baseline certification for disbursement vendors that handle sensitive claimant data at scale. A SOC 2 Type II audit, conducted by an independent CPA firm, verifies that the vendor’s security controls operated effectively over a sustained period, typically six to twelve months. SOC 2 Type I only tests whether controls exist at one point in time. Type II tests whether they work consistently over time.
What a good answer looks like: The vendor provides the most recent SOC 2 Type II report on request, with an audit period that ended within the last twelve months. The report scope covers the Trust Services Criteria most relevant to payments, including Security, Availability, and Confidentiality. The vendor can answer specific questions about exceptions, carve-outs, or qualified opinions.
What to watch for: A vendor that offers SOC 2 Type I when you ask for Type II, or that cites “pending” certification without a timeline, has not completed the sustained verification process. Treat it as a gap, not a technicality.
Question 2: How Is Claimant Data Encrypted?
Encryption is the foundational technical control protecting claimant data. Two layers matter: data in transit, meaning information moving between the claimant portal, vendor systems, and payment rails, and data at rest, meaning stored records, backups, and tax documents.
What a good answer looks like: The vendor uses TLS 1.2 or TLS 1.3 for data in transit, with strong certificate management and no unsupported legacy protocols. Data at rest uses AES-256 encryption. The vendor maintains documented key management procedures covering generation, rotation, revocation, and destruction. Encryption applies to all stored claimant records, not only payment data.
What to watch for: Vague answers referencing “bank-level security” without naming protocol versions or encryption standards. Vendors that cannot describe their key management process have not fully operationalized encryption governance.
Question 3: Is OFAC Screening Automated Before Payment?
OFAC screening checks payment recipients against sanctions lists maintained by the U.S. Treasury. OFAC compliance is a federal obligation because U.S. persons and covered entities cannot transact with blocked parties. Screening is the practical control vendors should use to prevent prohibited payments.
Manual screening, or screening only at registration, is weaker because sanctions lists change. Vendors that screen only at onboarding and not again before payment may miss updated sanctions listings. That creates avoidable compliance risk.
What a good answer looks like: Every disbursement recipient is screened before payment initiation, not only at registration. The platform uses current sanctions data. Potential matches trigger a payment hold, administrator alert, and documented review path. The vendor can produce a sample workflow showing how a flagged payment is handled.
What to watch for: Any description of sanctions screening as a one-time onboarding check. Any reliance on manual review for the majority of payments. Any inability to explain what happens when a possible match is detected.
Question 4: How Are Settlement Funds Segregated?
QSF compliance under IRC Section 468B requires settlement funds to be held in structures that are legally separate from the administrator’s or vendor’s operating accounts. Commingling settlement funds with operating funds creates legal, accounting, and court-reporting risk.
What a good answer looks like: The vendor maintains dedicated QSF-compliant accounts for each settlement engagement. Funds are held with an FDIC-insured banking institution and are not commingled with the vendor’s operating capital. The vendor can describe the account structure, name the banking partner, and explain how fund balances are reported.
What to watch for: Vendors that hold client funds in pooled accounts without per-client tracking. Inability to name the banking institution. Any workflow suggesting client funds pass through the vendor’s operating accounts before disbursement.
Question 5: What Identity Verification Is Used?
KYC verification helps prevent fraudulent claimants from receiving funds intended for legitimate settlement recipients. The verification process should confirm identity before any payment is released, not after.
What a good answer looks like: The platform validates government-issued ID, cross-references SSN or TIN information where appropriate, and confirms address information before approving a payout request. Verification workflows are documented and auditable. The vendor can explain how failed or flagged verifications are handled and when human review is available.
What to watch for: Identity verification treated as a single checkbox at registration instead of a workflow tied to payment release. Vendors that rely only on self-reported information without cross-reference validation.
Question 6: Do You Generate a Full Audit Trail?
Court-supervised disbursements require documentation that every payment was authorized, screened, verified, and executed correctly. A full audit trail also serves as the administrator’s primary defense in the event of a dispute, regulatory inquiry, or fraud allegation.
What a good answer looks like: The platform generates a timestamped, tamper-evident record of every event in the payment lifecycle: claimant registration, identity verification, sanctions screening, payment authorization, delivery confirmation, and exceptions. Audit records are accessible through an administrator dashboard and exportable for court reporting.
What to watch for: Audit logs that capture only payment outcomes without the underlying verification steps. Logs that cannot be exported. Any system where audit data is stored separately from the transaction record and requires manual reconciliation.
Question 7: What Is Your Breach Notification Policy?
A vendor that experiences a security incident must notify clients quickly enough for them to meet their own obligations to claimants, courts, regulators, and counterparties. Notification timelines matter because state breach notification laws often require disclosure to affected individuals within 30 to 90 days, while certain federal or sector-specific rules may impose shorter timelines.
What a good answer looks like: The vendor has a documented incident response plan with defined roles, escalation procedures, and a written commitment to notify the client within 72 hours of a confirmed breach, or sooner if required by law. The vendor can describe recent tabletop exercises or incident simulations. The plan includes communication templates and a designated client contact.
What to watch for: Incident response described as a general process without timelines. No documented escalation path. Inability to confirm whether an incident response exercise occurred in the past twelve months.
Question 8: How Do You Manage Sub-Vendor Risk?
A disbursement vendor’s security posture includes the security posture of every cloud host, payment processor, identity provider, and subprocessor it relies on. Third-party and fourth-party risk is now a central security issue for fintech and payment workflows.
What a good answer looks like: The vendor maintains an inventory of sub-vendors with access to claimant data or payment infrastructure. Sub-vendors are assessed before onboarding and reviewed on a recurring schedule. The vendor can explain how a security failure at a sub-vendor would be detected, contained, and communicated to clients.
What to watch for: No formal sub-vendor inventory. No annual review of sub-vendor security posture. Inability to name the cloud infrastructure provider or confirm equivalent certifications.
Question 9: What Are Your Data Retention Policies?
Claimant records contain sensitive PII that should not be retained indefinitely. At the same time, some records must be retained for tax, legal, court, or audit purposes. A vendor needs a documented policy that balances legal retention requirements with data minimization.
What a good answer looks like: The vendor applies defined retention schedules tied to legal requirements, often including multi-year retention for tax-related records. At the end of the retention period, data is deleted using a documented secure deletion method. The vendor can provide a sample retention schedule and explain whether deletion is automated or manually approved.
What to watch for: Data retained indefinitely with no documented policy. Deletion processes that are not audited or confirmed. No distinction between legally required retention and default storage.
Question 10: What Cyber Liability Coverage Do You Carry?
Cyber liability insurance signals two things: the vendor’s own assessment of residual risk and its ability to respond financially to a security incident. Insurance is not a substitute for security controls, but it is an important part of vendor risk management.
What a good answer looks like: The vendor carries cyber liability coverage scaled to the settlement size and claimant population. For high-volume engagements, $5 million or above is commonly recommended. The policy covers first-party breach response costs, third-party liability, claimant notification costs, and regulatory defense costs. The vendor can provide a current certificate of insurance.
What to watch for: Coverage limits that are materially below the risk level of the engagement. General commercial liability presented as cyber coverage. Policies that exclude incidents originating from third-party vendors.
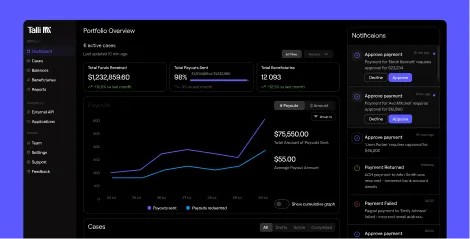
How Talli Addresses These Requirements
For claims administrators evaluating modern disbursement infrastructure, the Talli platform is built around the compliance controls of this security due diligence checklist targets. Talli is an AI-driven digital payments platform specializing in legal settlement disbursements, class action payouts, bankruptcy distributions, and mass payment distribution for law firms, claims administrators, and settlement providers.
SOC 2 Type II and encryption: Talli maintains SOC 2 Type II certification, with security controls aligned to the needs of high-volume legal disbursements. Claimant data is protected with strong encryption controls, including TLS for data in transit and AES-256 encryption for data at rest.
OFAC screening before payment release: Talli supports automated sanctions screening as part of the payment workflow. Recipients are screened before payment release, and potential matches can be held for administrator review with documentation added to the audit record.
QSF-compliant fund segregation: Settlement funds are held in dedicated, segregated structures through regulated banking partners, including Patriot Bank, N.A., Member FDIC. Client funds are separated from operating capital, helping preserve QSF ownership and support court-ready reporting.
Automated KYC tied to payment release: Identity verification is integrated into the payout workflow. Government ID validation, SSN or TIN checks, and address confirmation can occur before payment authorization. Flagged verifications route into documented exception workflows rather than informal manual bypasses.
Full audit transparency: Every transaction generates a timestamped audit trail covering claimant registration, identity verification, sanctions screening, payment authorization, delivery confirmation, and exception handling. Administrators can monitor activity through the dashboard and export records for court reporting.
Payout flexibility with compliance automation: Talli supports ACH, prepaid Mastercard, PayPal, Venmo, Amazon gift cards, and checks as fallback. Compliance automation, including KYC verification, OFAC screening, W-9 collection, and 1099 support, applies across payout methods.
Scale and track record: Talli is built to support campaigns from thousands to hundreds of thousands of recipients. Settlement campaigns can be launched in days rather than months, with real-time visibility into payout status, completion rates, exceptions, and fund flows.
How to Run the Vendor Review Process
This checklist works best as a structured intake document sent to candidate vendors before a call, followed by a review session to assess the quality of responses.
Step 1: Send the questions in writing. Require written responses to all ten questions before any demonstration or discovery call. Written responses create a documented baseline and reveal vendors that are not prepared for detailed security inquiry.
Step 2: Request supporting documentation. For each question, identify evidence that confirms the answer: the SOC 2 Type II report, certificate of insurance, incident response plan, sample audit trail export, sub-vendor inventory, and fund segregation documentation.
Step 3: Score on three dimensions. Evaluate each response on completeness, specificity, and documentation quality. A complete answer explains what the vendor does. A specific answer names systems, standards, and workflows. A documented answer proves it.
Step 4: Escalate gaps before contracting. Any disqualifying response should be addressed before the contract is signed. Security gaps are harder to remediate after the vendor already controls claimant data or settlement funds.
Step 5: Set a review cadence. Annual reassessment is the standard for critical vendors handling sensitive data and payment workflows. Build vendor review rights into the contract so future assessments do not require renegotiation. A structured vendor due diligence process should become part of the administrator’s operating model.
Warning Signs That Warrant Disqualification
Not every security gap is equal. Some represent immaturity that can be remediated. Others represent structural failures that should disqualify a vendor regardless of other strengths.
Disqualifying warning signs:
- No SOC 2 Type II certification and no clear timeline to achieve it
- Sanctions screening that is manual, periodic, or limited to onboarding
- Settlement funds held in operating accounts
- No documented incident response plan
- No breach notification commitment
- Inability to produce a certificate of cyber liability insurance
- No sub-vendor inventory for systems that touch claimant data
Gaps that require remediation commitments before signing:
- SOC 2 Type II report more than 18 months old
- Informal or undocumented sub-vendor review
- Data retention policy that exists but has not been audited
- Cyber liability coverage materially below settlement risk
- Audit logs that require manual reconciliation before court reporting
Responses that signal evasion:
- Redirection to marketing materials when asked for technical documentation
- Claims that security details are “proprietary” and cannot be shared under NDA
- Repeated assurances that the platform is secure without specifics
- Refusal to provide a sample audit export or incident response summary
A vendor that cannot answer this checklist clearly is already providing useful information. They are not ready to handle compliance-critical disbursements at scale.
Required Documentation Checklist
Before signing with any disbursement vendor, request these documents in writing. Verbal assurances are representations, not verification.
Disbursement Vendor Compliance: GDPR vs. U.S. Requirements
For settlement engagements involving European claimants or cross-border distributions, vendors may need to address GDPR requirements in addition to U.S. federal and state obligations.
Disbursement vendors operating in multi-jurisdiction engagements may need to satisfy U.S. sanctions law, state breach notification rules, IRS tax documentation standards, and GDPR obligations if EU personal data is involved. A vendor that cannot demonstrate compliance across the applicable frameworks is not equipped for cross-border settlement administration.
Talli Conclusion
Security due diligence for disbursement vendors is not a procurement formality. It is the most important risk management step a claims administrator can take before engaging a payout partner.
The ten questions in this checklist cover the categories that matter most: certification, encryption, sanctions compliance, fund segregation, identity verification, audit transparency, incident response, supply chain risk, data governance, and financial coverage.
Vendors that answer all ten with specificity and supporting documentation demonstrate operational maturity. Vendors that cannot are surfacing their gaps before they become your incidents.
Talli is built for administrators who need these controls embedded into the disbursement workflow from the start. Its platform combines digital payout options, QSF-aware fund segregation, automated compliance workflows, real-time tracking, and audit-ready reporting for legal settlement distributions.
Claims administrators who want to see how a purpose-built disbursement platform addresses these requirements can Book a Demo with Talli’s team.
Frequently Asked Questions
What is security due diligence for disbursement vendors?
Security due diligence for disbursement vendors is the process of evaluating a payout partner’s technical controls, compliance certifications, data governance practices, fund segregation model, and incident response capabilities before engaging them to process settlement funds or claimant disbursements. It differs from general vendor diligence because disbursement vendors handle claimant PII, payment credentials, tax documentation, and court-supervised funds.
What certifications should a disbursement vendor hold?
The minimum credible baseline is SOC 2 Type II certification, which verifies that security controls operated effectively over a sustained audit period. For payment-heavy engagements, administrators may also ask about PCI DSS where card data is handled and ISO 27001 where international operations are relevant. Certification alone is not enough. The report scope and control evidence matter.
Is OFAC screening required for settlement disbursements?
OFAC compliance is required because covered parties cannot transact with sanctioned individuals or entities. Screening is the practical control used to prevent prohibited payments. For settlement disbursements, screening should occur before payment release, not only at claimant registration, because sanctions data can change between onboarding and payout.
What is a QSF account and why does it matter?
A QSF, or Qualified Settlement Fund, is a fund structure established under Internal Revenue Code Section 468B to hold settlement proceeds separate from the defendant’s assets, administrator funds, or vendor operating accounts. QSF-compliant fund segregation matters because it prevents commingling, supports court reporting, and protects claimants from vendor financial risk.
How often should you reassess a disbursement vendor?
Critical vendors that handle claimant PII, payment credentials, or settlement funds should be reassessed annually. Reassessment should also be triggered by a material security incident, ownership change, infrastructure change, expired SOC 2 report, new payment rail, or change in sub-vendor risk.
What happens if a disbursement vendor experiences a breach?
The administrator’s obligations depend on the data involved and the states or jurisdictions where claimants reside. Many state breach notification laws require notice to affected individuals within 30 to 90 days. Some federal or sector-specific rules may impose different timelines. The vendor’s contractual breach notification commitment determines how quickly the administrator receives actionable information.
What documentation should you request before signing?
Request the current SOC 2 Type II report, cyber liability certificate, written incident response plan, sample audit trail export, fund segregation documentation, sub-vendor inventory, data retention schedule, and current banking confirmation. Written responses with supporting documentation are more reliable than verbal assurances.
How does GDPR affect disbursement vendor diligence?
GDPR may apply when settlement distributions involve EU or EEA personal data. For cross-border disbursements, administrators should confirm whether the vendor can support a Data Processing Agreement, appropriate transfer mechanisms, breach notification workflows, deletion rights subject to legal retention exceptions, and documented data minimization practices.

.svg)
.svg)

